AWS Identity and Access Management (IAM) is a web service that helps you securely control access to AWS resources. It controls who can sign in to your AWS infrastructure and who is authorized to use the resources (EC2, VPS, IoT, Cognito, and etc)
When I started earning AWS for the first, I had difficulties identifying the difference between Cognito and IAM. Cognito is a user management solution for your enterprise applications that also use IAM (Spring, JakartaEE, Angular, or any other application that you develop.)
Check this example: https://www.harshajayamanna.com/2019/10/aws-cognito-spring-complete-example.html
On the other hand, IAM is for the management of users in your AWS infrastructure.
Root User
When you sign up with AWS services for the first time, a Root user is created that has complete access to all AWS services and resources in the account.
AWS recommends that we should not use this account to continue day-to-day tasks, instead, the first step is to create the first IAM admin user and created other users with the required access level based on the requirements.
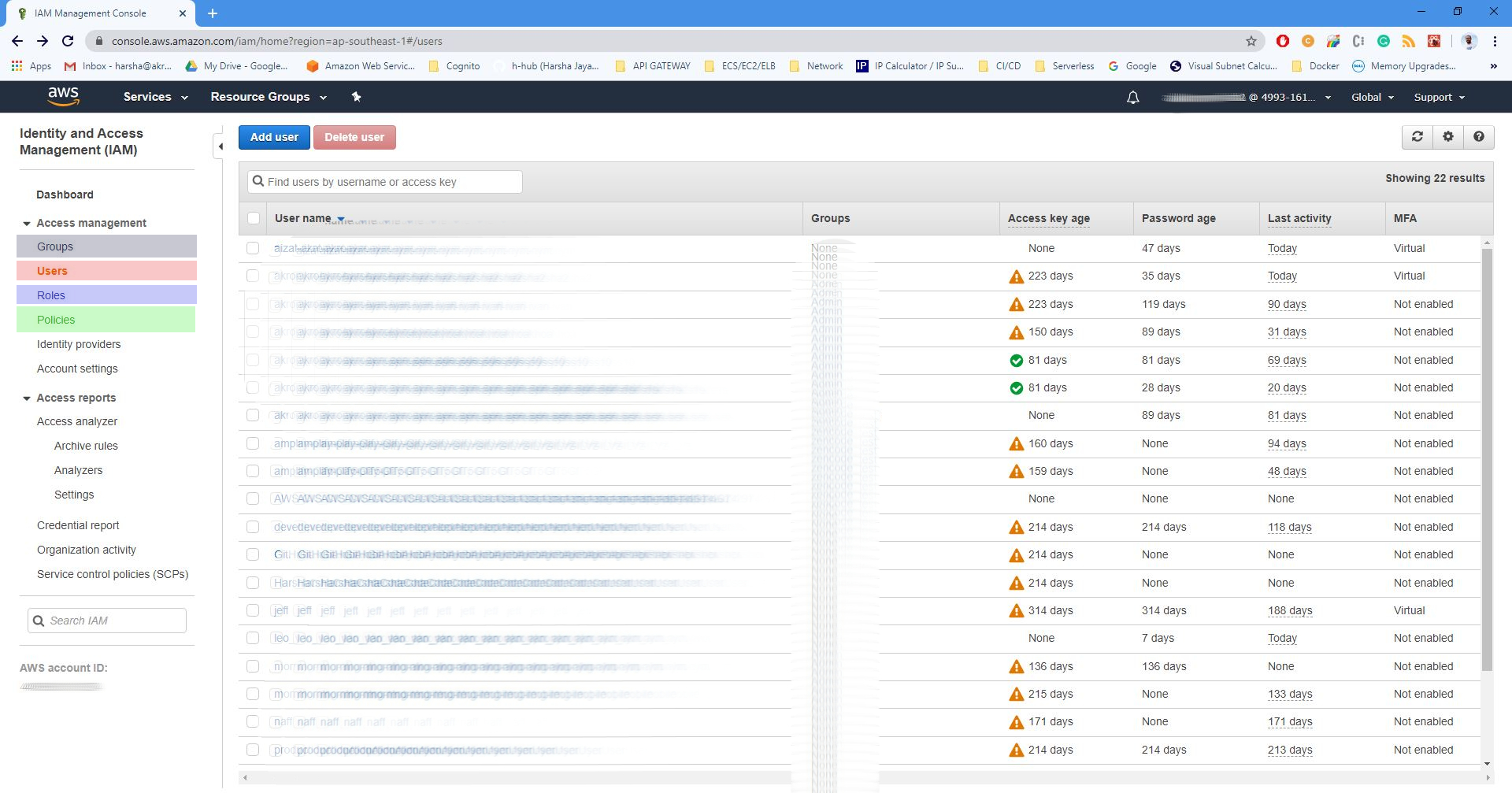
IAM Dashboard: From this dashboard, you can create IAM users, groups, roles, and policies.
AWS IAM Users
In this section, we are talking about IAM users. As described in the above section, the first IAM user is created by the root account.
IAM user is an entity that you create in AWS to represent the person or application that uses it to interact with AWS.
Since AWS has many functionalities and many interfaces (Web, CLI) there are several ways to access AWS services.
- A password can be used to access the AWS Management Console.
- Access keys can be used to make programmatic calls to AWS (AWS CLI, Powershell).
- SSH keys can be used to access AWS CodeCommit.
- SSL/TLS certificates that you can use to authenticate with some AWS services.
When creating an IAM user, the IAM admin user in the organization has to create the user and give required permission by attaching policies or by adding the user to a group.
AWS recommends that you put your users in groups and manage permissions through policies that are attached to those groups.
AWS IAM Policies
AWS policies can be attached to users, groups of users, roles, or AWS resources. Policies manage access.
Example:
{
"Version": "2012-10-17",
"Statement": {
"Effect": "Allow",
"Action": "s3:ListBucket",
"Resource": "arn:aws:s3:::file_bucket"
}
}The above policy will allow listing a single Amazon S3 bucket named file_bucket.
When a user or a role makes a request, AWS evaluates the policy to determine whether to allow or deny the request. There are several types of policies and based on the requirement, you can utilize those policies.
AWS IAM Groups
An IAM group is a collection of IAM users. By using groups, you can put similar users together and assign them policies. It is a way to attach policies to multiple users at one time.
Example: Admins of the AWS services can be put into an "ADMIN" group. Software Engineers can be put into a group called "SE", while Firmware developers can be put into a group called "FDEV".
AWS Roles
AWS Role has policies attached to it but not associated with one person. A role can be assumed by any user who needs it but cannot be assigned to Users or Groups.
Example:
Amazon Cognito identity pools provide temporary AWS credentials for users who are guests. If your systems allow the users who are not logged-in to send emails, you will have to use Identity pools and allow them to assume roles with permission to access AWS SES to send emails.
Conclusion
Most people, who are new to AWS might find that IAM topics are hard to understand. But it is not, you just need to read the documentation properly and understand the connections, similarities, and differences between IAM Users, groups, roles, and policies.
References
- https://docs.aws.amazon.com/IAM/latest/UserGuide/id_groups.html
- https://docs.aws.amazon.com/IAM/latest/UserGuide/id_users.html
- https://docs.aws.amazon.com/IAM/latest/UserGuide/id_users_create.html
- https://docs.aws.amazon.com/IAM/latest/UserGuide/introduction.html
- https://docs.aws.amazon.com/IAM/latest/UserGuide/id_root-user.html
- https://docs.aws.amazon.com/IAM/latest/UserGuide/getting-started_create-admin-group.html
- https://docs.aws.amazon.com/IAM/latest/UserGuide/access_policies.html
- https://docs.aws.amazon.com/IAM/latest/UserGuide/id_roles_compare-resource-policies.html

Comments
Post a Comment